-
Paper Information
- Next Paper
- Paper Submission
-
Journal Information
- About This Journal
- Editorial Board
- Current Issue
- Archive
- Author Guidelines
- Contact Us
International Journal of Networks and Communications
p-ISSN: 2168-4936 e-ISSN: 2168-4944
2016; 6(5): 87-97
doi:10.5923/j.ijnc.20160605.01

A Low Latency cross Layer based Scheduling Technique for Wireless Mesh Networks
Asha C. N.1, T. G. Basavaraju2
1VTU Research Scholar, Department of Electronics and Communication Engineering, Acharya Institute of Technology, Bangalore, India
2Professor in Computer Science and Engineering Department, Govt. SKSJTI, Bangalore, India
Correspondence to: Asha C. N., VTU Research Scholar, Department of Electronics and Communication Engineering, Acharya Institute of Technology, Bangalore, India.
| Email: |  |
Copyright © 2016 Scientific & Academic Publishing. All Rights Reserved.
This work is licensed under the Creative Commons Attribution International License (CC BY).
http://creativecommons.org/licenses/by/4.0/

The growth of smart phone technology have resulted in increased number of multimedia application which requires low latency service delivery and coverage which the existing wireless technology could not handle due to power limitation imposed by Wireless Local Area Network (WLAN) regulatory body. To address this wireless mesh networks (WMNs) was standardized by task group S to support multihop based communication. Reducing packet delivery latency in existing multihop WMN is one of key issues that need to be addressed. The existing methodology induces high data delivery latency due to inability to address the hidden and exposed node problem in multihop WMN environment. Many approaches have been developed to optimize the Medium Access Control (MAC), hidden node and exposed node detection algorithm in recent time to better utilize slot and reduce latency. The existing method adopts contention based method to address the collision caused by the hidden node problems which result in improper utilization of slot, which result in bandwidth wastages. Node classification technique for reutilizing slot will aid in improving network performance by reducing latency. As it is seen the latency plays a significant part in improving the performance overall throughput of a network. This work proposes an efficient device classification based MAC scheduler by adopting a cross layer design to reduce the data delivery latency. The experiments are conducted to evaluate mean network latency and data delivery latency by varying depth of tree for varied network size and density. The outcome shows that the proposed approach perform better than existing CSMA/OCA in term of network data delivery latency.
Keywords: Cross-Layer, IEEE 802.11, Scheduling, WMN
Cite this paper: Asha C. N., T. G. Basavaraju, A Low Latency cross Layer based Scheduling Technique for Wireless Mesh Networks, International Journal of Networks and Communications, Vol. 6 No. 5, 2016, pp. 87-97. doi: 10.5923/j.ijnc.20160605.01.
Article Outline
1. Introduction
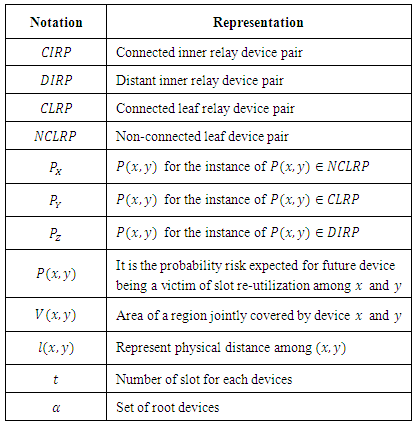
- WMN is considered to be the future paradigm of wireless access technology due to its low cost of deployment and high coverage. The WMN can support various application services are as follows intelligent public transportation system, wireless internet broadband services, disaster management etc… The IEEE 802.11WLAN (wireless local area network) is a most sorted standard due to its unlicensed operating bands of 2.4 GHz and 5 GHz. Due to the regulatory enforcement limitation of transmission power result in limiting the transmission range of WLAN [1, 23]. Nevertheless the requirement of such large wireless network is in huge demand in various areas such as office, home, university, campuses etc… The demand for growth of low latency service cannot be addressed by existing single hop communication of IEEE 802.11WLAN. To achieve a low latency service delivery it requires a multihop services, to achieve this Task Group S [1, 2] has been working to standardize the IEEE 802.11 to achieve multi hop association by optimizing the routing capabilities and frame forwarding at medium access control layer. The 802.11s standardization brings a new cost effective and secure communication.WMN establishes an ad-hoc infrastructure as in Figure 1, i.e. it is self-configured and self-organized, with the devices in the network can join and leave a network and still maintaining the mesh connectivity. The 802.11s mesh networks are made of two forms of devices namely mesh clients and mesh routers. Like the 802.11 wireless device it also support routing proficiency for gateway tasks along with that the mesh router contain an added routing functionalities to provision mesh infrastructure. The WMN adopts a multi-hop transmission [2]; which can achieve a better coverage by a mesh router with reduced power for transmission. To provide flexibility of WMN the wireless mesh router are fitted with multiple wireless interfaces built on various wireless access technologies.
 | Figure 1. The Architecture of Wireless Mesh Networks |
1.1. Design Issues and Challenges in 802.11s Wireless Mesh Network
- The difficulties faced at the time of Mesh network designing process given as [2, 3, 23]. Mesh Connectivity is an important factor in order to guarantee network self-organization, reliable connectivity, and topology control protocols are required. Topology conscious routing and MAC protocols can efficiently enhance the performance of mesh networks. At the different interval of network predication of number of subscriber is an important issues and difficult task. For that reason predication of load which is generated on the mesh network also get difficult. Channel capacity and performance varying according to the system parameters. Scalability is an important factor and necessities of Wireless mesh networks. The network performances will degrades badly without provision of scalability i.e. for varying network sizes and density. For instance, routing strategy may not be suitable or find difficulties in finding a cost effective routing path, loss of connectivity, and MAC protocols may see degradation in throughput performance. To ensure the scalability in Wireless mesh networks, all strategies from the medium access layer to the application layer need to be designed considering scalability.The paper organization is as follows: In Section two the literature review are briefly described. In section three, the proposed scheduling techniques are discussed. Section four the simulation result are obtained and evaluated with existing methodologies. The last section the paper is concluded with future works.
2. Literature Survey
- Providing an end-to-end low latency service delivery guarantee for end user in multi hop wireless mesh network is one of major challenges that need be addressed. Various methodologies have been proposed in recent time to address the issue such finding bandwidth or low latency link for transmission, addressing the hidden node problem in multihop environment to reduce collision and QoS delivery for end user since the WMN has large coverage area. In recent years routing in WMN to achieve high throughput and low latency service delivery in multi hop wireless environment is been a hot research trend [24, 25]. In multi-hop environment the packet are forwarded through multiple intermediate devices when the source and destination are not within the range of communication area. Many approaches have been proposed to route the packet in an efficient manner from source to destination [26, 27]. The performance of these methodologies is not efficient since these strategies did not consider the hidden and exposed node problem that exists in multi-hop wireless mesh networks. The hidden node problem in multi-hop wireless mesh networks depends on carrier sense of source devices and the device within the communication range of particular end devices [28, 29]. If the carrier sense of source device [29] are within the interference range destination device will result in packet collision at the destination devices due to hidden node problem. Due to large coverage of wireless mesh network will result in increased rate of collision of packet as compared with WLAN as a result the network capacity is affected.The IEEE 802.11s protocol adopt CSMA/CA as its MAC protocol [30] which significantly degrades the performance of methodology that adopted CSMA/CA as it’s MAC due to hidden node problem. To address the hidden node problem that underlying IEEE 802.11s employs the Clear to Send/Request to Send (CTS/RTS) mechanism, but this increases the communication overhead in the mesh network due to transmission of beacon update packets [31]. To address the latency due to hidden node in contention based protocol, the contention less based TDMA based approach have been adopted in recent times which consider fixed traffic pattern for scheduling but the drawback these protocol is over allocation of bandwidth.To address [32] proposed a two-stage link scheduling which adopted a dynamic link scheduling mechanism to overcome the NP-Hard problem of optimal throughput algorithm [33]. They did not consider slot reutilization technique and when network become large it suffer from linear search problem in associating links which induces high network overhead. In [17] they proposed special reuse for hidden and exposed node; they adopted power optimization mechanism to address the interference caused by hidden and exposed nodes, there model improved the throughput but implementation of such model requires the MAC layer to be altered, and continuous measurement of signal interference to noise ratio (SINR) and channel error transmission result in communication overhead in control channels thus induces latency for channel access.To overcome all these problems that exists in designing a low latency wireless mesh network, this work present a low latency scheduling technique by adopting slot reutilization technique strategy based on device classification methodology [22] which is presented in section 3 below.
3. Proposed Node Classification Based Slot Reutilization Scheduling Model
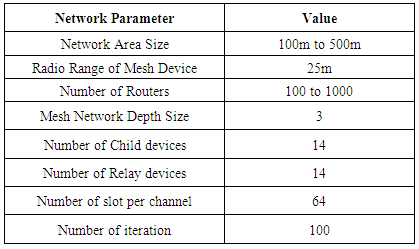
- To provide a low latency Quality of Service (QoS) for WMN’s which suffer from hidden node problem due to its large coverage area, slot reutilization is an effective method to reduce latency for channel access for data delivery but will induces channel collision. To address this work present a scheduling technique by adopting slot reutilization technique based on device classification method [22] to reduce the latency of the mesh network. The benefit of slot reutilization is that it utilizes the unutilized slot of its neighbour devices for transmission of its packets. The utilization of this unutilized slot will aid in improving the utilization of bandwidth more efficiently. This help in providing a cost effective service delivery platform as bandwidth availability is very limited. Though slot reutilization improves in utilizing bandwidth more efficiently but it induces collision due to hidden device problem. As both devices might try to access same channel or deny channel access thus incur collision and increases latency. The latency is the most critical part in providing efficient service delivery (improving throughput). Minimizing latency for channel access is most desired. Device classification plays a significant role in addressing hidden node problem for efficient slot reutilization and minimizing latency. Classification of device pair is done based on tree structure and neighbourhood and parenthood relationship. Device pair classification is done below in terms of x and y and this device pair classification is shown in Figure 2.
 | Figure 2. The proposed device classification model for IEEE 802.11s wireless mesh network |
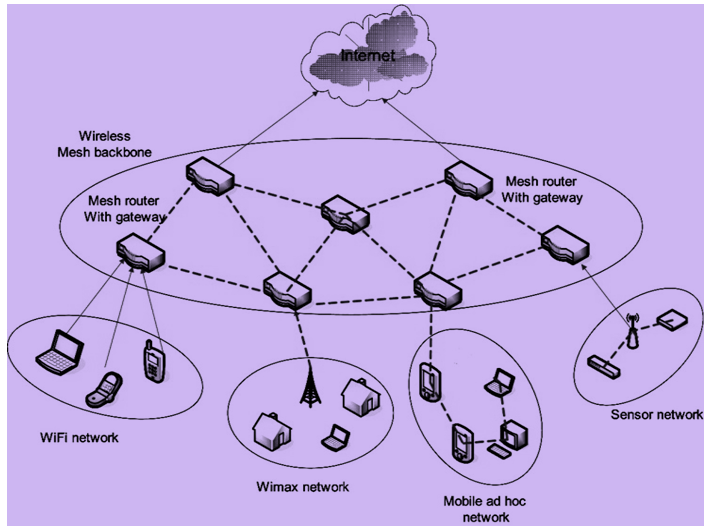
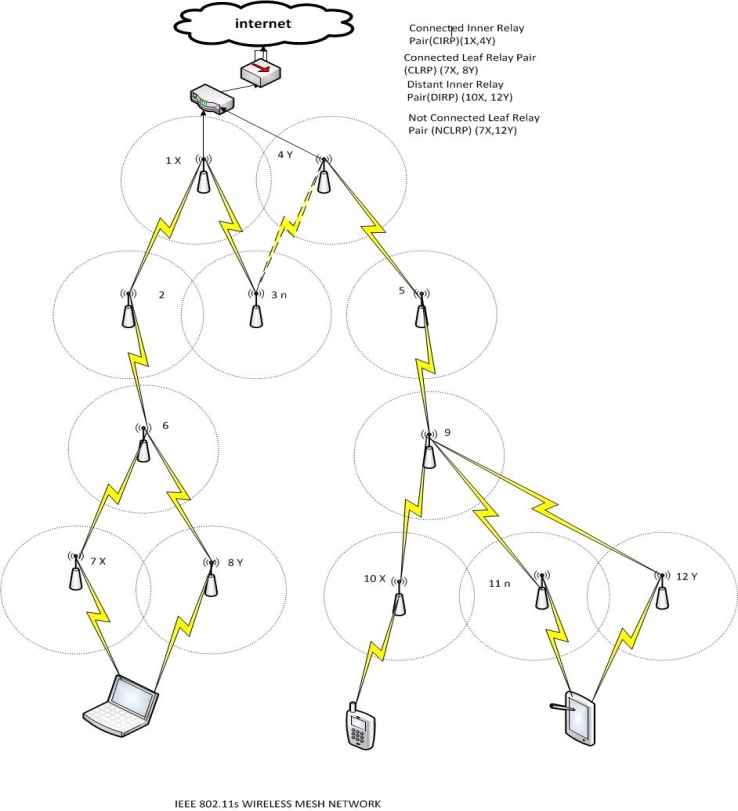
3.1. Proposed Node Classification based Scheduling approach
- The mesh router slot is set to zero initially for node join operation. When a device x needs to a join a wireless mesh network it primarily needs to search the node join operation of adjacent mesh router which are currently present in the wireless mesh tree. Let α represent a collection of root contenders of wireless mesh router. The mesh router that cannot allow a leaf node is removed first by using α. The root selection strategy is then applied by node x to sort. In this case the x root device must be the adjacent wireless mesh router that hast the least depth parameter. In our strategy to break the ties, the adjacent mesh router is chosen that has highest number of slot and depth parameter. Once the α is sorted, the device x choose a root device form α by following strategy.Firstly, get the first α of α, compute weather x can join with α as mesh router. If α has lesser than the maximum number of leaf node of wireless mesh router or gateway amongst its leaf, and has a depth of maximum depth of tree -2 or lesser, and selectTranSlot(α,x) which gets a transmission slot t, then x joins with α. If it fails to join the first α, it checks the next devices of α till all the devices of α is computed. To verify whether a device x can join as mesh router or as a mesh router end device the depth check is considered.Secondly, the device x will join a mesh network as mesh router end device of α's first device if it fails to identify device in α. Below the flow diagram of the proposed node classification based slot reutilization based scheduling is shown, where flow diagram 4 shows the slot selection selectTranSlot(α,x) and flow diagram 3 represent device pair classification computation retPairClass(x,y).
3.2. Transmission Latency Optimization Algorithm
- Let us consider a WMN of m nodes. Let
 represent a set of MAP’s and Access routers. The active user nodes of the WMN are
represent a set of MAP’s and Access routers. The active user nodes of the WMN are  . The WMN is represented using a tree structure and number of possible children of any node is
. The WMN is represented using a tree structure and number of possible children of any node is  . The tree structure is defined as
. The tree structure is defined as  , where
, where  represent tree depth. The user nodes communicate to the nearest access router and data is transmitted using a hop based mechanism over the tree structure of
represent tree depth. The user nodes communicate to the nearest access router and data is transmitted using a hop based mechanism over the tree structure of  nodes. Probability that a communication from the
nodes. Probability that a communication from the  to
to  node suffers due to slot-reutilization is
node suffers due to slot-reutilization is 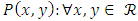 . The slot success probability is therefore,
. The slot success probability is therefore, 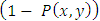 . Transmission latency is dependent of slot success probability. Higher successful slot transmission probabilities reduce latency. Hop to hop transmission is considered for WMN here. Let
. Transmission latency is dependent of slot success probability. Higher successful slot transmission probabilities reduce latency. Hop to hop transmission is considered for WMN here. Let  , represents the physical neighbors of
, represents the physical neighbors of  node. The next hop node amongst
node. The next hop node amongst  nodes is selected using following objective function
nodes is selected using following objective function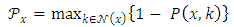 | (1) |
 transmission from
transmission from  to
to  node is represented as
node is represented as  . The total transmission latency observed is computed using
. The total transmission latency observed is computed using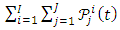 | (2) |
|
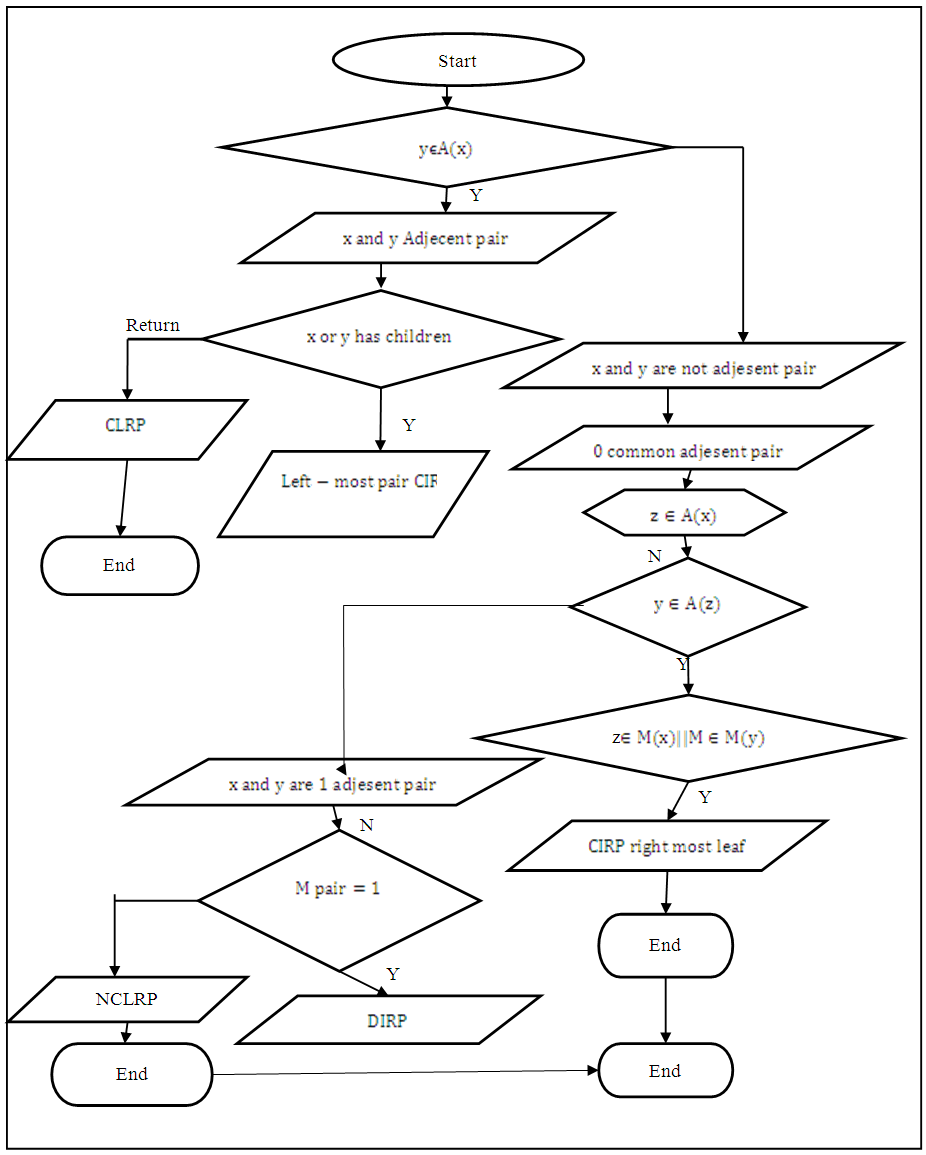 | Figure 3. Flow diagram for retPairClass(x,y) |
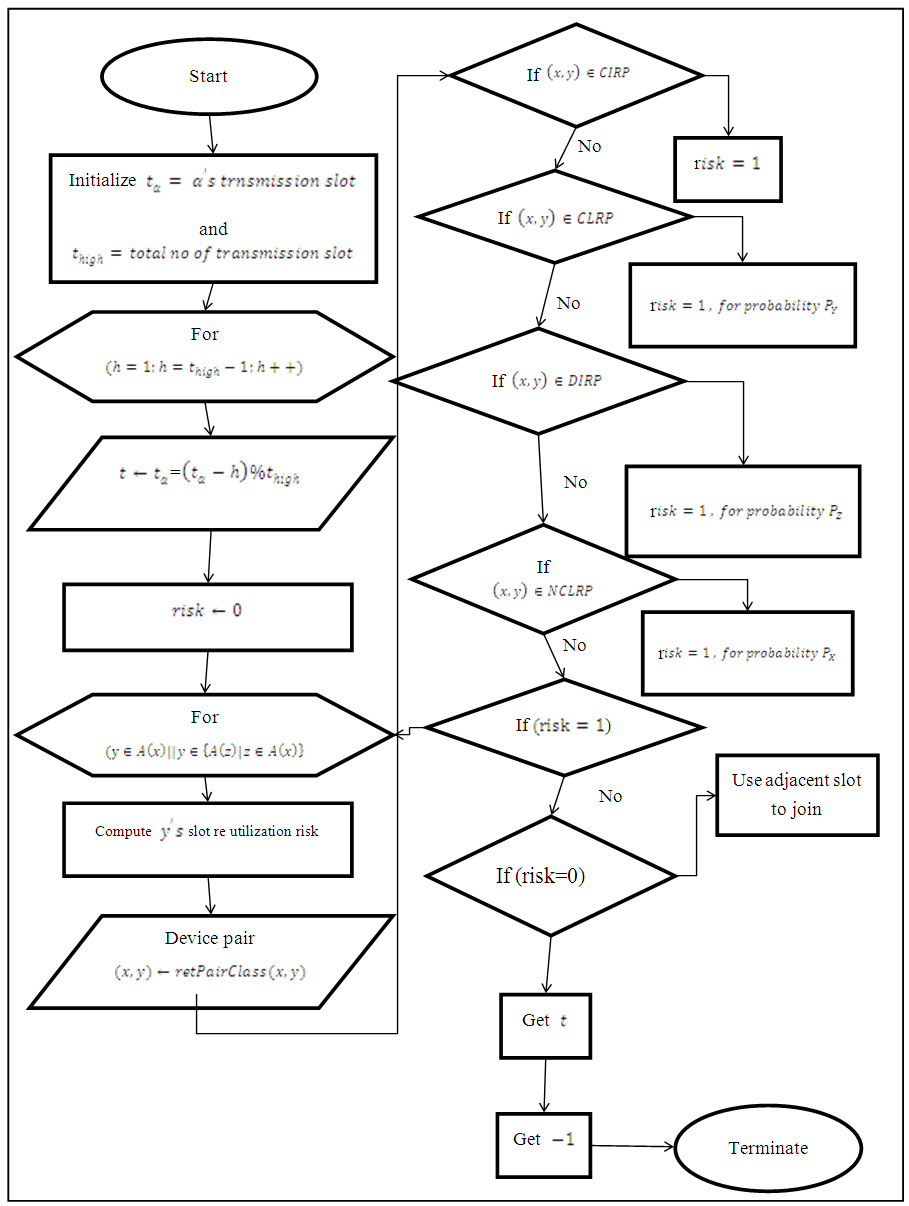 | Figure 4. Flow diagram for selectTranSlot(α,x) |
4. Experimental Analysis
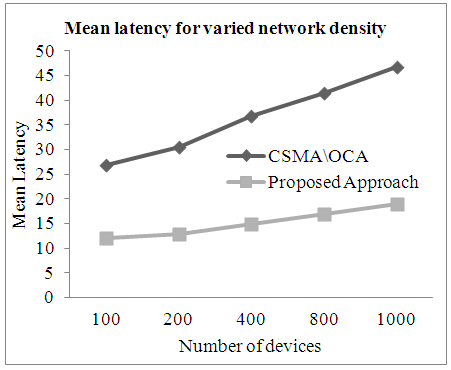
- The Simulation study is done using windows 7 enterprises has 64-bit operating system it contain i-5 class Intel processor with 8GB of RAM. Visual Studio 2015, Dot net frame work 4.0 and the programming language used is VC++ and C#. This work conducted simulation study for mean latency and means maximum latency for channel slot re-utilization by varying the network size and network density, and also for packet delivery latency by varying depth of mesh tree and is compared with the existing CSMA/OCA [17]. In experimental study network size is varied as 100, 200, 300, 400 and 500 meter and network density is varied as 100, 200, 400, 800 and 1000 devices. The mean latency is the mean of mean latency of all run and mean maximum latency (MML) is the mean of maximum latency with respect to simulation run which can be defined as follows
 | (3) |
|
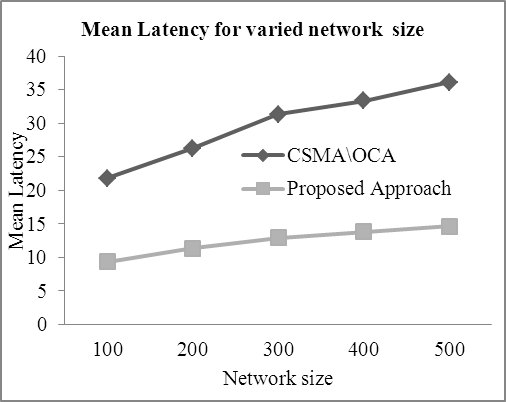 | Figure 5. Mean latency achieved for varied network size |
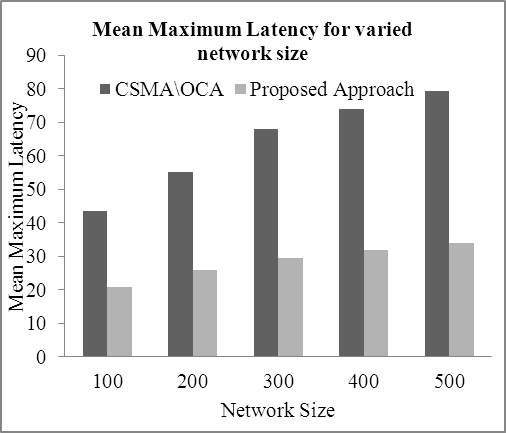 | Figure 6. Mean Maximum Latency for varied network size |
 | Figure 7. Mean Latency achieved for varied network density |
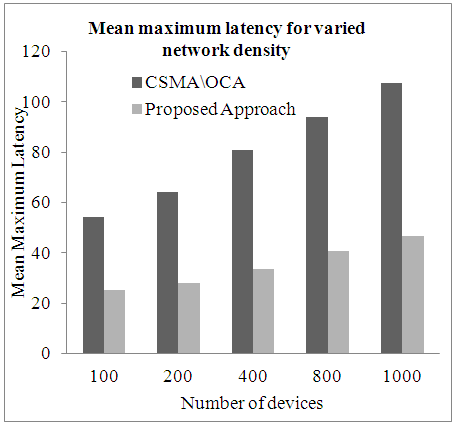 | Figure 8. Mean maximum latency achieved for varied network density |
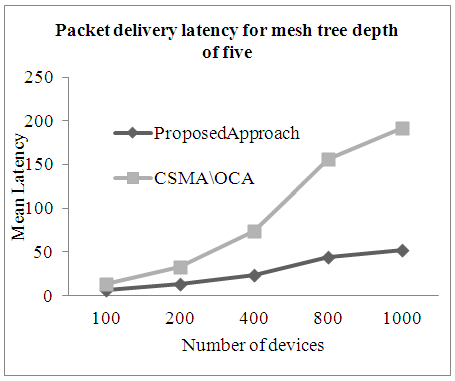 | Figure 9. Packet delivery latency for tree depth size of five |
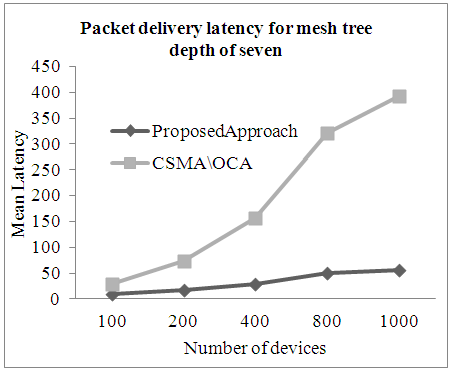 | Figure 10. Packet delivery latency for mesh tree depth size of seven |
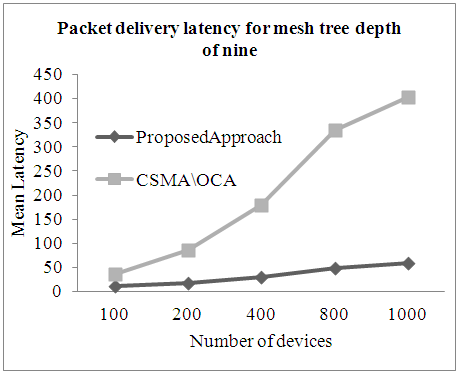 | Figure 11. Packet delivery latency for mesh tree depth size of nine |
5. Conclusions
- This work presented a low latency service delivery model for wireless mesh network. As demand for multimedia based application service is growing at rapid pace which requires a low latency service delivery. In wireless mesh network reducing the latency is a key factor to meet QoS necessities of the end user. This work presented a Low latency cross layer based MAC scheduling scheme by adopting a node classification technique for slot reutilization. The slot reutilization model addresses the hidden node problem by adopting node classification method which reduces collision thus improving the performance of service delivery of proposed model. Experiment are conducted to evaluate the performance of latency of network by varying network size and density and also packet delivery latency for varied depth of mesh tree size is compared with existing CSMA/OCA. The outcome shows the proposed model reduce the network mean maximum latency by 55.17%, mean latency by 58.19% for varied network size scenario, and reduce mean maximum latency by 56.13% and mean latency by 56.32% for varied network density and reduce mean packet delivery latency by 74.34% for varied mesh tree depth size over CSMA/OCA. In future work considers evaluating the performance of proposed model in hybrid wireless mesh network and also simulation study of throughput analysis.
 Abstract
Abstract Reference
Reference Full-Text PDF
Full-Text PDF Full-text HTML
Full-text HTML